In 2025, a foreign cyberespionage group silently moved through a major corporation’s network — using nothing more than a compromised VPN credential. No brute force. No malware dropped at the perimeter.
Just one unpatched gateway and overly permissive access rights. Within hours, they had lateral access to sensitive infrastructure.
That incident is not an exception. It is a pattern.
Virtual Private Networks remain one of the most widely deployed security tools on the planet, yet they are also among the most actively targeted. Understanding how modern VPN architecture actually reinforces — and sometimes undermines — your cyber defenses is no longer optional for security-conscious individuals and organizations.
How Modern VPN Architecture Reinforces Your Cyber Defenses
A well-architected VPN does several things that meaningfully reduce your exposure to threats.
Encrypted tunnels in transit. At its core, a VPN creates an encrypted channel between your device and a destination network. This protects data from interception on untrusted networks — public Wi-Fi, shared ISP infrastructure, or hostile network environments.
Modern VPNs using WireGuard or IKEv2/IPSec with AES-256 encryption make passive eavesdropping essentially impractical.
IP masking and traffic obfuscation. A VPN replaces your real IP address with the server’s IP, making attribution harder for adversaries conducting reconnaissance. This limits passive profiling of your network activity.
Split tunneling and policy enforcement. Enterprise VPN configurations can enforce that all traffic — or only specific categories of traffic — is routed through the secure tunnel. Combined with firewall rules and intrusion prevention systems (IPS), this creates a controlled egress point rather than an open door.
Zero Trust integration. Modern VPN deployments increasingly pair with Zero Trust Network Access (ZTNA) principles — verifying identity at every access request rather than assuming trust once someone connects. This is a major architectural improvement over legacy models that granted broad network access upon authentication.
Attack Surfaces a VPN Can Help Harden — And Where It Can Fall Short
This is where honest security analysis matters. A VPN is not a silver bullet.
Where VPNs Add Real Hardening
| Attack Vector | How VPN Helps |
| Man-in-the-Middle (MITM) | Encrypted tunnel prevents packet interception |
| ISP surveillance | Masks browsing activity and DNS queries |
| Public Wi-Fi snooping | Protects unencrypted traffic on shared networks |
| IP-based targeting | Hides real IP from reconnaissance scans |
| Data exfiltration in transit | Encryption prevents readable data capture |
Where VPNs Consistently Fall Short
The harder conversation is about VPN limitations. According to the Zscaler ThreatLabz 2025 VPN Risk Report, VPNs typically grant users broad network access instead of application-specific permissions, increasing the attack surface and allowing lateral movement if credentials are compromised.
Several critical failure points stand out:
- Credential compromise. Once an attacker obtains valid VPN credentials — through phishing, credential stuffing, or dark web purchases — the tunnel itself becomes their access vector. The Colonial Pipeline attack in 2021 traced back to a single VPN account without multi-factor authentication.
- Unpatched vulnerabilities. In 2025, VPNs occupied a strange paradox: adoption and spending were soaring, but their security reputation had never been shakier. Known CVEs in popular VPN appliances have been weaponized within days of disclosure.
- Lateral movement. Once VPNs were compromised, attackers could pivot laterally, disable defenses, and deploy ransomware at speed. Without proper network segmentation, a compromised VPN session grants access to far more than intended.
- Third-party access risks. 69% of organizations fear that third-party VPN access could introduce exploitable security gaps.
The core architectural problem: traditional VPNs were designed for occasional remote access by trusted employees — not for securing today’s distributed, hybrid-cloud, multi-vendor environments.
What to Prioritize in VPN Selection for Security-Minded Users
Not all VPNs are built equally. Whether you are an enterprise security team or an individual user serious about privacy, these criteria should drive your evaluation.
1. Encryption Standards and Protocol Support
Leading services use AES-256 encryption, which is considered military-grade and virtually unbreakable. Protocols like WireGuard, OpenVPN, and IKEv2 provide speed and security without compromising either. Avoid any provider still offering PPTP as a connection option — it is cryptographically broken.
2. Verified No-Logs Policy
A VPN provider that logs your activity can expose it — voluntarily or under legal compulsion. Look for independently audited no-logs claims, not self-declared ones. Jurisdiction matters too: providers based outside the Five Eyes, Nine Eyes, and 14 Eyes intelligence-sharing alliances face less legal pressure to hand over user data.
3. Patch History and Vendor Accountability
Select a VPN vendor with a strong track record of vulnerability patching, and request a software bill of materials (SBOM) to validate that third-party code is up-to-date and secure. A vendor who quietly patches critical CVEs is less trustworthy than one who discloses and documents them publicly.
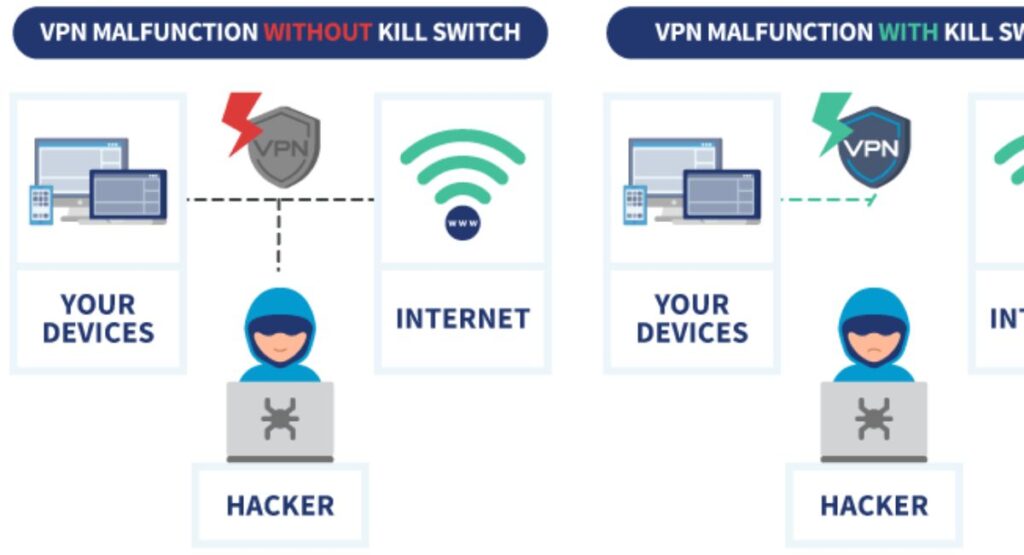
4. Kill Switch and Leak Protection
A kill switch cuts your internet connection if the VPN tunnel drops, preventing your real IP from being exposed in a reconnection gap. Verified DNS and IPv6 leak protection is equally important — many VPNs encrypt traffic but still leak DNS queries to the default resolver.
5. Multi-Factor Authentication Support
NSA and CISA recommend employing multi-factor authentication, regular and timely patching and updating, and disabling any features that are not specifically VPN-related. MFA is a non-negotiable control, particularly for enterprise deployments.
Use Cases Where VPN Strategy Matters in Real Security Contexts
Remote Workforce Security
Employees connecting from home networks, hotel Wi-Fi, or coffee shops expose corporate traffic to interception. A properly configured VPN with enforced MFA and endpoint compliance checks significantly reduces this exposure.
According to the 2025 Verizon DBIR, stolen credentials were involved in 22% of all confirmed breaches. Adding MFA to VPN access directly addresses this attack vector.
Whistleblowers, Journalists, and High-Risk Individuals
For individuals operating under surveillance risk — journalists, activists, researchers in hostile jurisdictions — a VPN combined with Tor provides layered anonymity. ProtonVPN’s Secure Core architecture, for instance, routes traffic through privacy-hardened data centers before exit, protecting against network-level adversaries.
Healthcare and Financial Compliance Environments
Regulated industries must protect data in transit. A VPN enforcing TLS 1.3 and AES-256, with full audit logging routed to a SIEM platform, satisfies baseline requirements under HIPAA and PCI-DSS for securing data transmitted over public networks.
Third-Party and Contractor Access
Vendors and contractors frequently need limited access to internal systems. A VPN that supports application-specific access controls — rather than full network access — contains the blast radius if a third-party account is compromised.
Best Practices to Harden VPN Usage
Following CISA, NSA, and industry guidance, here are the most impactful hardening steps:
1. Enforce MFA on every VPN account. No exceptions. A password alone is no longer sufficient defense against credential theft.
2. Patch aggressively. Per a CISA advisory, exploitation of remote access vulnerabilities can occur within 9 to 13 days of disclosure, which makes monthly patching cycles dangerously slow for internet-facing VPN gateways. Treat VPN patches as emergency updates.
3. Restrict port exposure. Limit port exposure to what is minimally required — for example UDP/500, UDP/4500 and protocol type 50 for ESP. Disable unused VPN features and cryptographic algorithms to prevent exploitable weaknesses.
4. Implement network segmentation. Prevent lateral movement by ensuring VPN users land in a segmented network zone with least-privilege access to only the resources they need — not a flat network where they can reach everything.
5. Route all VPN traffic through a security stack. All VPN traffic should pass through a full security stack en route to and from the enterprise network, including a web application firewall (WAF) and intrusion prevention system (IPS).
6. Centralize logging and monitoring. Session logs, authentication events, and anomalous access patterns should feed into a centralized SIEM system. Silent VPN sessions that persist for unusual durations or access unexpected resources are early indicators of compromise.
7. Disable split tunneling by default in high-risk environments. While convenient, split tunneling allows non-VPN traffic to bypass security controls entirely. In environments handling sensitive data, enforce full-tunnel configurations.
8. Conduct regular access reviews. Dormant accounts — especially for departed employees or former contractors — are a common attack vector. Automate account lifecycle management and deactivate VPN access immediately upon offboarding.
Conclusion
A VPN is not a security solution in isolation — it is one layer in a defense-in-depth strategy. When architected correctly, regularly patched, and hardened with MFA, network segmentation, and continuous monitoring, it meaningfully reduces your exposure to interception, reconnaissance, and credential-based attacks.
But the threat landscape has evolved faster than most VPN deployments. Ransomware groups and nation-state actors have made VPN vulnerabilities a primary entry point precisely because so many organizations treat “VPN deployed” as “security achieved.” That gap is where breaches happen.
Use your VPN intentionally. Choose vendors with verifiable security practices. Layer it with Zero Trust controls. Audit it regularly. A VPN that you actively manage and harden is a genuine asset to your security posture — one you neglect is a liability waiting to be exploited.
FAQs
Does a VPN make you completely secure online?
No. A VPN encrypts your traffic and hides your IP, but it cannot protect you from phishing, malware, credential theft, or endpoint compromises. It is one layer of defense, not a complete security solution.
Can attackers break VPN encryption?
Modern AES-256 encryption is computationally unbreakable with current technology. Attackers do not break the encryption — they target misconfigured gateways, unpatched vulnerabilities, or stolen credentials to bypass it entirely.
Is a free VPN safe to use for security purposes?
Generally, no. Free VPNs often monetize user data, apply weak encryption, and lack independent audits. For any security-sensitive use case, a paid provider with verified no-logs policies and regular third-party audits is essential.
How often should enterprise VPN software be patched?
Critical patches affecting internet-facing VPN gateways should be applied within 48–72 hours of release. CISA data shows that exploitation of disclosed VPN vulnerabilities can begin within 9 to 13 days of public disclosure — making monthly patch cycles inadequate.
Should I use a VPN on my mobile device?
Yes, especially on public or untrusted networks. Mobile devices are frequent targets for MITM attacks on open Wi-Fi. A VPN with a kill switch ensures your traffic remains encrypted even during brief network drops.
- Visit InfozCelebritys for more blogs.

I’m Muhammad Zeeshan – a guest posting and content writing expert with 4 years of experience.